Learning Paths
Last Updated: April 8, 2026 at 19:30
Symmetric vs Asymmetric Encryption Explained: Key Differences, Examples, Use Cases, and When to Use Each
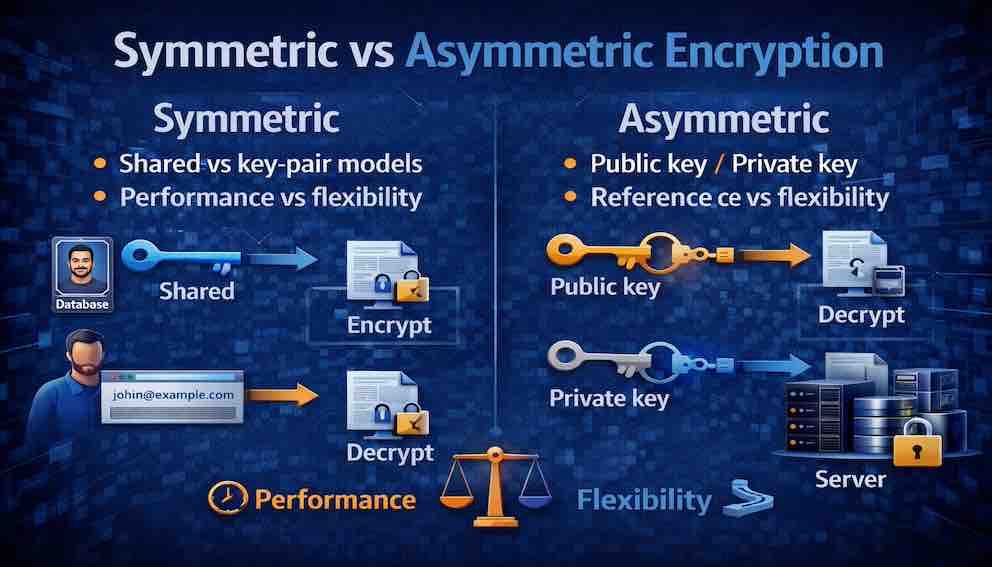
Shared secrets, public-private key pairs, performance trade-offs, and how modern systems combine both in real-world architectures.
Every secure system you use — HTTPS, SSH, encrypted messaging — relies on two fundamentally different kinds of encryption working together. Symmetric encryption uses one shared key, making it fast and ideal for bulk data. Asymmetric encryption uses a public-private key pair, solving how strangers establish trust without prior contact. Understanding the difference is the foundation of practical security.
A Story: The Lockbox and the Mailbox
Imagine you need to send a secret message to a friend across town. You have two ways to protect it.
The lockbox. You put your message in a metal box, lock it with a padlock, and send it. But your friend cannot open it — they do not have the key. So before you send anything, you must meet in person and hand over a copy of the key. Now you can exchange locked boxes freely. The same key locks and unlocks.
This is symmetric encryption. One key does everything. Fast and simple, but sharing the key safely is hard.
The mailbox. Imagine a mailbox with a wide-open slot. Anyone can drop a letter in. But once inside, only the owner can retrieve it, using their private key. You never share a key. You just find your friend's public mailbox, drop your message in, and walk away.
This is asymmetric encryption. A public key for locking, a private key for unlocking. No key to share beforehand, but slower and more complex.
Both protect messages. Both solve different problems.
The lockbox is fast but requires you to share the key first. The mailbox needs no prior arrangement but is slower.
Every encryption system you use — HTTPS, SSH, encrypted messaging — relies on one of these approaches, or combines both. Understanding the difference is where practical security begins.
Part One: What Is Symmetric Encryption?
Symmetric encryption is a cryptographic method where the same secret key is used to both encrypt and decrypt data.
If you know the key, you can lock and unlock data. If you do not know the key, you can do neither.
The core characteristics:
- One key. A single secret key controls both operations.
- Fast. Symmetric encryption is computationally efficient, making it practical for encrypting large volumes of data.
- Requires key distribution. Both parties must possess the same key before they can communicate securely. That key must be shared through a secure channel.
- Key management complexity. If many pairs of users need to communicate, each pair needs its own unique key. The number of keys grows quickly — specifically, n × (n-1) / 2 unique keys for n parties.
Part Two: Symmetric Encryption in Practice
Symmetric encryption is used wherever large volumes of data need to be encrypted efficiently.
Full disk encryption. When your laptop's storage is encrypted (BitLocker on Windows, FileVault on macOS), symmetric encryption is doing the work. The drive is locked with a single key derived from your password. The data is far too large for asymmetric encryption to be practical.
Database encryption. Sensitive columns — credit card numbers, medical records, national identification numbers — are typically encrypted with symmetric keys. The key itself is stored separately or retrieved from a key management service at runtime.
TLS session data. When you visit an HTTPS website, the page content, your form submissions, and the images are all protected with symmetric encryption. Asymmetric encryption is used only during the initial handshake to exchange a temporary symmetric key; after that, everything switches to fast symmetric encryption for the remainder of the session.
File encryption. Tools like GPG, OpenSSL, and 7-Zip use symmetric encryption when you protect a file with a password. Your password is derived into a key, and that key encrypts the file contents.
Wi-Fi security (WPA2, WPA3). The traffic between your device and a wireless router is protected with symmetric encryption. The network password is used to derive an encryption key shared between your device and the access point.
Part Three: The Key Distribution Problem
Symmetric encryption has a structural weakness that cannot be solved with better mathematics. Before two parties can communicate securely, they must share the same secret key. Getting that key to both parties safely is the hard part.
Meet in person. Alice and Bob exchange the key face to face. Secure, but impractical at scale.
Use a trusted courier. Alice sends the key via a trusted messenger. This introduces cost, delay, and another point of trust.
Use asymmetric encryption to exchange the key. This is the solution used by TLS, SSH, and most modern protocols. Asymmetric encryption solves the distribution problem. Symmetric encryption then handles the actual data.
Pre-shared keys. In controlled environments — corporate VPNs, IoT device fleets — keys are loaded onto devices before deployment. This works when the set of devices is fixed and managed in advance.
The key distribution problem is exactly why asymmetric encryption was such a significant breakthrough. It solved something that symmetric encryption alone never could.
Part Four: What Is Asymmetric Encryption?
Asymmetric encryption is a cryptographic method that uses a mathematically related pair of keys — a public key and a private key — where data encrypted with one key can only be decrypted with the other.
You publish your public key openly. You keep your private key secret. Anyone can use your public key to encrypt a message. Only you, with your private key, can decrypt it.
The core characteristics:
- Two keys. A public key for encryption, a private key for decryption.
- No key distribution problem. Public keys can be shared openly without compromise.
- Slower. Asymmetric encryption is computationally expensive — typically 100 to 1,000 times slower than symmetric encryption for the same data volume.
- Larger ciphertext. Encrypted output is significantly larger than the original plaintext.
- Enables digital signatures. The same key pair can be used in reverse — sign with the private key, verify with the public key — to prove authenticity and integrity.
Why asymmetric encryption works at all:
This is the part that seems almost magical. How can you give someone a key (the public key) that lets them encrypt a message, but that same key cannot decrypt the message they just encrypted? The answer lies in a special class of mathematical problems.
Imagine you have two numbers: 6,107 and 9,371. Multiplying them is easy — anyone with a calculator can do it in seconds. But if I give you the product — 57,239,497 — and ask you to tell me which two numbers I multiplied to get it, that is much harder. You would have to test possibilities. For small numbers, it is still easy. But if the numbers are hundreds of digits long, the multiplication is still easy, but the reverse process — factoring — is practically impossible with current computers.
This is the heart of asymmetric cryptography. The mathematics are one-way: easy to compute in one direction, extremely difficult to reverse. The two most popular asymmetric algorithms today — RSA and ECC — are both built on this one-way principle. RSA uses the factoring problem just described. ECC uses a different but similar one-way problem called the elliptic curve discrete logarithm problem. These are not implementation tricks. They are the theoretical foundation that makes asymmetric encryption possible. The security of every RSA or ECC key you generate rests on the fact that no one knows a fast way to solve these problems.
Part Five: Asymmetric Encryption in Practice
Asymmetric encryption is not used to encrypt bulk data. It is too slow for that. Instead, it handles specific tasks where its unique properties are essential.
TLS handshake. When your browser connects to an HTTPS server, the handshake uses asymmetric encryption to agree on a temporary symmetric session key. Once that key exists, both sides switch to symmetric encryption for all subsequent traffic.
Email encryption (PGP, S/MIME). Your software fetches the recipient's public key and uses it to encrypt the message. Only the recipient, holding the corresponding private key, can decrypt it. No password needs to be shared in advance.
Digital signatures. You hash a message and encrypt that hash with your private key. Anyone holding your public key can decrypt the hash, recompute it from the message, and confirm both the origin and integrity. This is how JWT signatures, code signing, and document signing work.
SSH key-based authentication. When you connect to a server via SSH, the server challenges your client to prove it holds the private key corresponding to an authorized public key. Your client signs a challenge. The server verifies that signature. No password is transmitted.
Certificate Authorities. Certificate Authorities (CAs) sign TLS certificates with their private keys. Your browser ships with a list of trusted CA public keys. When a website presents its certificate, your browser verifies the CA's signature to confirm it is talking to the legitimate server and not an impersonator.
Part Six: The Core Trade-Off
The choice between symmetric and asymmetric encryption is a trade-off between performance and flexibility.
Symmetric encryption uses a single shared secret. It is very fast. It handles bulk data efficiently. Key sizes are small — 128 to 256 bits. Ciphertext is roughly the same size as the plaintext. Its weakness is that keys must be pre-shared through a secure channel, and the number of keys required grows with the number of communicating parties.
Asymmetric encryption uses a public/private key pair. It eliminates the key distribution problem entirely. It enables digital signatures. But it is slow — often 100 to 1,000 times slower — produces much larger ciphertext, and requires larger keys (2,048 to 4,096 bits for RSA, though ECC achieves equivalent security with much smaller keys). It is never used for bulk data.
The practical rule: use symmetric encryption when you already have a secure way to share keys and need to encrypt large amounts of data. Use asymmetric encryption when you need to communicate without prior arrangement, or when you need to prove identity.
In practice, most systems use both.
Part Seven: Hybrid Encryption — The Best of Both Worlds
Almost every modern secure communication system uses hybrid encryption, combining the strengths of both approaches.
How it works:
First, the two parties use asymmetric encryption to securely exchange a temporary symmetric key. This solves the distribution problem without any pre-arranged secret. Then, once both sides hold the shared symmetric key, they switch to fast symmetric encryption for all actual data transfer.
Where you see it:
TLS/HTTPS. Your browser and the web server use asymmetric cryptography (RSA or ECDH) during the handshake to agree on a session key. All web traffic then flows over AES.
SSH. Host and user authentication use asymmetric keys (RSA or ECDSA). The session itself uses symmetric encryption.
PGP/GPG. When you send an encrypted email, PGP generates a random symmetric key, encrypts the message with it, then encrypts only the symmetric key with the recipient's public key. Both are sent together.
Signal and WhatsApp. The Signal Protocol uses asymmetric encryption for initial key exchange and identity verification, then symmetric encryption for message content.
Hybrid encryption is the practical answer to a practical problem: use asymmetric where it is essential (key exchange, identity), and symmetric where it is strong (bulk data, performance).
Part Eight: When to Use Each — A Decision Framework
Use symmetric encryption when:
- You are encrypting large volumes of data (databases, disk volumes, files, network streams)
- You have a secure and managed way to distribute and store keys
- Both parties are known in advance and can be provisioned with keys
- Performance is a priority
- You do not need to prove identity — you already know who you are talking to
Examples: full disk encryption, database column encryption, Wi-Fi traffic, VPN tunnels, TLS session data after the handshake.
Use asymmetric encryption when:
- You need to communicate with someone without a prior key exchange
- You need to verify identity (digital signatures, certificate validation)
- You need to distribute a public key openly without risk
- The data being encrypted is small (symmetric keys, message hashes, short tokens)
Examples: TLS handshake, email encryption (PGP/S/MIME), code signing, SSH authentication, JWT signatures.
Use hybrid encryption when:
- You need secure communication over an untrusted network
- You need both secure key exchange and efficient bulk encryption
- You are building any kind of secure messaging system, VPN, or web application
Examples: HTTPS, SSH, PGP, Signal, WhatsApp, most commercial VPNs.
Quick decision guide:
- Encrypting a database column? Use symmetric (AES).
- Exchanging keys for a TLS session? Use asymmetric (RSA or ECDH) then hybrid.
- Signing a JWT? Use asymmetric (private key to sign, public to verify).
- Encrypting a file for yourself? Use symmetric (your password derives the key).
- Encrypting an email to someone you have never met? Use asymmetric (their public key).
Part Nine: Key Size and Strength
Before we compare specific numbers, let us clarify what "key size" actually means.
A key is just a very large random number. The key size tells you how many bits that number contains. A 128-bit key is a random number that can be any value between 0 and about 340 undecillion — a number so vast it is difficult to even comprehend. A 256-bit key is exponentially larger — there are more possible 256-bit keys than there are atoms in the observable universe.
When an attacker tries to break encryption without the key, they have to guess. This is called a brute-force attack. They try one possible key, then another, then another. The larger the key size, the more guesses they need. Double the key size does not mean double the guesses — it means exponentially more guesses. A 256-bit key is not twice as hard to guess as a 128-bit key. It is roughly 340 undecillion times harder. This is why key size is the most basic measure of cryptographic strength.
Symmetric key sizes (AES):
128-bit keys are strong. Brute-forcing all possible 128-bit keys is beyond the reach of any known technology and will remain so for the foreseeable future. 256-bit keys are stronger still and considered quantum-resistant for now — relevant because future quantum computers will reduce the effective security of symmetric keys by half (Grover's algorithm), making 256-bit keys the safe long-term choice.
The rule: 128 bits is the minimum. Use 256 bits for anything that needs to remain secure over a long time horizon.
RSA key sizes:
RSA requires much larger keys because the underlying mathematics are different. A brute-force attack on RSA does not guess the key directly — it tries to factor a large number. The difficulty grows with the size of that number. 1,024-bit RSA is broken and must not be used. 2,048 bits is the current minimum and is appropriate for most applications. 3,072 or 4,096 bits is preferred for high-security environments or where certificates have long validity periods.
Elliptic Curve Cryptography (ECC):
ECC achieves the same security as RSA with much smaller keys because the underlying mathematical problem is harder. A 256-bit ECC key is roughly equivalent in security to a 3,072-bit RSA key. A 384-bit ECC key is roughly equivalent to 7,680-bit RSA. This is why ECC (specifically ECDH and ECDSA) has largely replaced RSA in modern TLS configurations. The keys are smaller, so operations are faster, certificates are smaller, and power consumption is lower.
For new systems, prefer ECC unless compatibility with legacy infrastructure requires RSA.
The quantum future:
Future quantum computers threaten both RSA and ECC. NIST is finalizing post-quantum algorithms, but for now, AES-256 remains the safest symmetric choice, and hybrid systems will transition their asymmetric components when standards mature.
Part Ten: Performance Considerations
The performance gap between symmetric and asymmetric encryption is substantial, and it explains why hybrid encryption is universal rather than optional.
Symmetric encryption is measured in gigabytes per second on modern hardware. AES-256 with hardware acceleration (AES-NI instructions, present in virtually all modern CPUs) can encrypt at 1 to 5 GB per second per core. This makes it practical for disk encryption, high-throughput database operations, and network traffic at any realistic volume.
Asymmetric encryption is measured in thousands of operations per second. RSA-2048 typically performs tens of thousands of encryptions per second, but only a few hundred decryptions per second. (Decryption is slower because it requires the computationally expensive private key operation.) This is orders of magnitude slower than AES.
What this means in practice: encrypting a 1 GB file with AES takes a fraction of a second. Doing the same with RSA would take minutes or longer, and produce a ciphertext many times larger than the original. This is not a theoretical concern — it is why you never use asymmetric encryption for bulk data.
Part Eleven: Key Management
The hardest part of cryptography is not encryption. It is key management.
Symmetric encryption has one major challenge: getting the same secret key to both parties securely. If you store the key next to the encrypted data, a breach compromises both. If you send the key over email or check it into source code, it is effectively public.
Asymmetric encryption solves the distribution problem but introduces its own challenges. Private keys must never be exposed. If a private key is stolen, every message encrypted to the corresponding public key is at risk. And how do you know a public key actually belongs to who it claims to? This is the Public Key Infrastructure (PKI) problem — solved by certificate authorities, but worth knowing exists.
Practical solutions for real systems:
- Cloud KMS (AWS KMS, Azure Key Vault, Google Cloud KMS) manages keys in hardened infrastructure. Your application calls the service to encrypt or decrypt; the raw key never reaches your servers.
- Hardware Security Modules (HSMs) are physical devices that store keys and perform cryptographic operations without ever exposing the key material. Keys never leave the HSM in plaintext.
- Secrets management tools (HashiCorp Vault) centralize secret storage, enforce access controls, and automate key rotation.
For most applications starting out, a cloud KMS is the right balance of security and operational simplicity. Save HSMs for compliance requirements or extreme threat models. And never, ever hardcode keys in source code.
Part Twelve: Common Mistakes
Using asymmetric encryption for bulk data. Encrypting a large file directly with RSA is slow and produces enormous output. The correct approach is hybrid: generate a random symmetric key, encrypt the file with it, then encrypt only the symmetric key with RSA.
Using symmetric encryption without solving key distribution. Hardcoding a symmetric key in source code, configuration files, or environment variables accessible to many people defeats the purpose. Use a key management service, or use asymmetric encryption to distribute keys dynamically.
Confusing encryption with signing. RSA supports both, but they are different operations. Using a private key to "encrypt" data is signing, not encryption. Using these operations interchangeably leads to systems that appear to work but provide none of the intended guarantees.
Using undersized keys. RSA-1024 is broken. Do not use it. The minimum for RSA is 2,048 bits. For symmetric encryption, 128-bit AES is the floor.
Storing keys alongside encrypted data. If an attacker who steals your encrypted database also finds the encryption key in a nearby configuration file, the encryption accomplished nothing. Keys and encrypted data must be stored and controlled separately.
Skipping key rotation. A key that has been in use for years has likely been handled by many people, copied to many systems, and present in many backups. Rotate keys regularly to limit the blast radius of a compromise.
Part Thirteen: Where Each Fits in the Security Chain
Both approaches appear throughout the layers of any secure system.
Asymmetric encryption handles trust and identity:
The TLS handshake uses asymmetric cryptography to establish trust and exchange session keys. Digital signatures — JWT tokens, software releases, document signing — rely on asymmetric key pairs. SSH key-based authentication proves user identity without transmitting a password. PGP email encryption lets anyone send you a confidential message without prior contact.
Symmetric encryption moves the data:
After the TLS handshake, every byte of web traffic travels under AES. Database encryption, disk encryption, and file encryption all use symmetric keys. VPN tunnels carry traffic encrypted symmetrically. Session tokens, when encrypted at rest, typically use symmetric keys.
The pattern is consistent: asymmetric encryption builds the trust and solves the distribution problem. Symmetric encryption handles the volume.
Closing: The Lockbox and the Mailbox Revisited
Return to the two approaches from the opening.
The lockbox — symmetric encryption — is fast and simple. One key locks and unlocks. But getting that key to your friend safely is a real problem. You must meet in person, trust a courier, or solve it some other way.
The mailbox — asymmetric encryption — is elegant. No prior arrangement. Anyone can drop a message in. Only the owner can retrieve it. But it is slower, more complex, and not designed for large payloads.
The real world does not choose one. It uses both.
You use the mailbox to deliver the key to the lockbox. Once your friend has the key, you switch to the lockbox for everything else. The mailbox solves the distribution problem. The lockbox handles the volume.
This is TLS. This is SSH. This is PGP. This is how secure communication works at scale.
Understanding each approach in isolation is necessary. Understanding when to reach for each is practical. Understanding how they work together is the foundation of building systems that are actually secure.
About N Sharma
Lead Architect at StackAndSystemN Sharma is a technologist with over 28 years of experience in software engineering, system architecture, and technology consulting. He holds a Bachelor’s degree in Engineering, a DBF, and an MBA. His work focuses on research-driven technology education—explaining software architecture, system design, and development practices through structured tutorials designed to help engineers build reliable, scalable systems.
Disclaimer
This article is for educational purposes only. Assistance from AI-powered generative tools was taken to format and improve language flow. While we strive for accuracy, this content may contain errors or omissions and should be independently verified.
