Learning Paths
Last Updated: April 2, 2026 at 12:30
What Is RBAC (Role-Based Access Control)
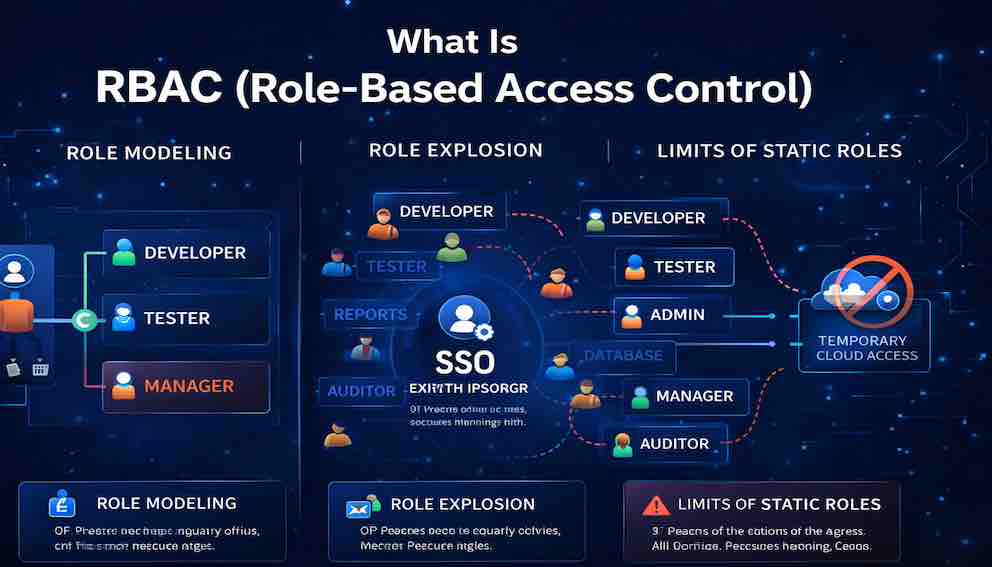
Role modeling, the role explosion problem, and the limits of static roles in modern systems
Role-Based Access Control is the most widely used authorization model in the world — and for good reason. It maps naturally to how organizations think, reduces administrative overhead, and provides a solid foundation for managing who can do what across complex systems. But RBAC has limits: as organizations grow, roles multiply, permissions bloat, and the model buckles under its own complexity. This article covers how RBAC works, how to design roles that don't collapse into chaos, and when you've outgrown static roles entirely
A Story: The Hospital
Imagine you work in a large hospital — a sprawling organization with thousands of employees. Doctors, nurses, surgeons, anesthesiologists, radiologists, pharmacists, lab technicians, administrators, billing specialists, and IT staff. Every person needs access to different parts of the hospital and different patient records.
A doctor needs to see patient charts, prescribe medications, and order tests. A nurse needs to administer medications, record vitals, and update patient status. A pharmacist needs to see prescriptions but not the full patient chart. A billing specialist needs to see insurance information but not medical history. A radiologist needs to view imaging results.
Now imagine that the hospital had to manage access for each person individually. Every time a new doctor joined, someone in IT would have to manually configure access to patient records, prescription systems, scheduling, messaging, and a dozen other applications. Every time a nurse changed departments, someone would have to update their permissions across every system.
This is the problem that Role-Based Access Control — RBAC — was designed to solve.
Instead of assigning permissions to each individual, the hospital defines roles. A doctor role has certain permissions. A nurse role has different permissions. When a new doctor joins, they are simply assigned the doctor role. When a nurse moves from surgery to pediatrics, they keep the nurse role — their permissions follow them.
RBAC is the most widely used authorization model in the world. It powers everything from hospital systems to cloud infrastructure to enterprise software. But it is not perfect. As organizations grow, roles multiply. Permissions become bloated. And eventually, the system collapses under its own complexity.
This article explains RBAC — how it works, why it is so popular, where it breaks down, and how to evolve beyond it when your needs outgrow static roles.
Part One: What Is RBAC?
Role-Based Access Control (RBAC) is an approach to authorization that grants permissions to users based on their assigned roles, rather than assigning permissions directly to individual users.
In RBAC, a role is a collection of permissions. A user is assigned one or more roles. The user inherits all permissions associated with those roles.
This simple indirection — user → role → permissions — is what makes RBAC powerful. It allows you to manage permissions at the role level, not the user level. When a new user joins, you assign them an existing role. When permissions change, you update the role once, and all users with that role inherit the change automatically.
The core components of RBAC are:
- Users — the individuals accessing the system
- Roles — collections of permissions with meaningful names (like "Doctor" or "Auditor")
- Permissions — the ability to perform specific actions on specific resources (like "view patient chart" or "edit prescription")
- Assignments — the mapping of users to roles, and roles to permissions
In practice, this looks like:
If Bob is a nurse, he gets the nurse role with a different set of permissions. If Carol is an administrator, she gets the admin role. The system does not need to know who Alice is as an individual. It only needs to know her role.
Part Two: Why RBAC Is So Widely Used
RBAC became the dominant authorization model for several good reasons.
It matches how organizations think. Organizations naturally group people by function — doctors, nurses, managers, administrators, customers. RBAC mirrors this structure. It is intuitive to say "a doctor can prescribe medication" rather than "Alice can prescribe medication, and Bob can prescribe medication, and Carol can prescribe medication..."
It simplifies administration. Without RBAC, adding a new user requires manually configuring permissions across dozens of systems. With RBAC, you assign the appropriate role. When a role's permissions need to change, you update it once and every user with that role gets the change automatically.
It enforces separation of duties. RBAC allows you to define roles that should not be combined. For example, the same person should not both create invoices and approve payments. By creating separate roles for invoice creators and payment approvers, you can enforce that no single user holds both — or audit the rare cases where they do.
It scales reasonably well. For small to medium organizations, 10–20 roles can cover all functions. This is manageable. Adding a new user is trivial. Adding a new application requires mapping its permissions to existing roles.
It is supported everywhere. Most enterprise systems — databases, cloud platforms, operating systems, SaaS applications — support RBAC natively. AWS IAM has roles. PostgreSQL has roles. Kubernetes has RBAC. This ubiquity makes RBAC the path of least resistance in most environments.
Part Three: The Core RBAC Models
RBAC is not a single specification. It is a family of models. Understanding these models helps you choose the right level of sophistication for your needs.
Core RBAC
This is the simplest form. Users are assigned roles. Roles have permissions. Nothing more.
A blog platform with roles for Author, Editor, and Admin is a textbook example. Authors can write and edit their own posts. Editors can edit any post. Admins can manage users and settings.
Hierarchical RBAC
Roles can inherit permissions from other roles, reflecting organizational structure.
In a hospital, a Senior Doctor role might inherit all permissions from the Doctor role, then add permissions for supervising residents and approving complex procedures. Hierarchical RBAC reduces duplication — you define a base role with common permissions, then create specialized roles that extend it.
Constrained RBAC
Constrained RBAC adds separation of duties rules. Certain role combinations are prohibited.
For example, the same user cannot hold both a "Create Invoice" role and an "Approve Payment" role. If someone tries to assign both, the system prevents it or flags it for review. This is critical for compliance with regulations like SOX (Sarbanes-Oxley) that require segregation of financial duties.
Symmetric RBAC
Symmetric RBAC adds the ability to query permissions in both directions. You can ask: "Which users have this role?" and also "Which roles does this user have?" and "Which permissions does this role grant?" This sounds obvious, but many systems only support one direction of query — and that gap becomes painful at audit time.
Part Four: Role Modeling — Designing Good Roles
The success of RBAC depends entirely on how well you design your roles. Bad role design leads to role explosion, permission bloat, and security holes.
Principles of Good Role Design
Model functions, not individuals. A role should represent a job function, not a person. If you find yourself creating a role called "Alice's Special Role," something has gone wrong. Roles should be reusable across multiple users.
Keep roles focused. Each role should have a clear, limited set of permissions. A role called "FullAccess" is a red flag — it suggests you have not thought through what access is actually needed.
Use role hierarchies sparingly. Inheritance is powerful but can become confusing. If a permission is granted through multiple inheritance paths, it becomes hard to trace why a user has it. Use hierarchies for clear organizational structures, not as a shortcut to avoid defining permissions precisely.
Separate functional roles from administrative roles. A user may have a functional role (like "Doctor") that gives them access to patient data, and an administrative role (like "Department Head") that gives them access to scheduling and management functions. These should be separate roles, independently assignable.
Use naming conventions that reflect intent. Role names should be meaningful to both technical and non-technical stakeholders. "PatientDataViewer" is less clear than "Nurse." If a role exists for a specific external integration, name it accordingly — like "Integration_Salesforce_ReadOnly."
Common Role Categories
Most systems benefit from thinking in three broad categories.
Functional roles reflect what the user does in the application. These are tied to business functions: Customer, PremiumCustomer, SupportAgent, Moderator, ContentCreator.
Administrative roles reflect what the user can do to the system itself — responsibilities tied to operations: SystemAdministrator, SecurityAuditor, BillingManager, UserAdmin.
Application-specific roles reflect integration patterns and are often assigned to service accounts rather than human users: APIClient_ReadOnly, ReportGenerator, WebhookConsumer.
Part Five: The Role Explosion Problem
The biggest challenge with RBAC is role explosion — when the number of roles grows uncontrollably from a manageable set of 10–20 into hundreds or thousands. Every combination of permissions becomes its own role. Every edge case spawns a new one. The system becomes unmanageable.
Why Role Explosion Happens
Fine-grained permissions. As your system grows, you add more granular permissions. You start with "can view patient data." Then "can view cardiology data only." Then "can view cardiology data for patients under 18." Then "can view cardiology data for patients under 18 in the outpatient clinic." Each new dimension of granularity multiplies the number of possible permission combinations, and if you create a role for each combination, you get exponential growth.
Multiple applications. When RBAC spans multiple applications, the combinatorial explosion worsens. A user needs access to CRM, ERP, HR, and billing systems. Each application has its own permission set. The number of role combinations across all applications becomes staggering.
No hierarchy discipline. Without careful use of role hierarchies, developers create new roles for every slight variation instead of building on existing ones. A role called "DoctorCardiology" appears. Then "DoctorCardiologyAttending." Then "DoctorCardiologyFellow." The proliferation continues quietly until it becomes a crisis.
One-off requirements. A single user needs a special combination of permissions. Instead of reviewing the role model, an administrator creates a new role just for that user. That role persists long after the user leaves.
The Symptoms of Role Explosion
You are experiencing role explosion when you have hundreds of roles but only a handful have more than one assigned user; when you cannot explain why a particular role exists; when new users need multiple roles because no single role covers their needs; when audits reveal roles with no assigned users — so-called zombie roles; and when permission changes require updating dozens of roles instead of one.
How to Prevent Role Explosion
Regularly review and prune roles. Set a cadence for role review. Remove unused roles. Merge roles with overlapping permissions. Archive roles created for temporary purposes.
Use role hierarchies instead of creating new roles. When you need a variation of an existing role, create a child role that inherits from the parent and adds the specific permission needed. This keeps base roles clean and makes the hierarchy explicit.
Consider attribute-based approaches for fine-grained permissions. If you find yourself creating roles like "DoctorCardiologyOutpatientWeekend," you have outgrown RBAC for that decision. At this level of granularity, attributes — department, specialty, shift — should determine access, not roles. This is ABAC (Attribute-Based Access Control), covered in the next Article.
Use multiple role assignments. Instead of creating a role that combines "Doctor" and "Cardiology" and "Outpatient" into one, assign users separate roles for each dimension. The combination of roles determines their access without multiplying the role count.
Automate role assignment. If roles are being created manually for each new user, you have a process problem. Automate role assignment based on attributes from your HR system. When a user's department changes, their roles update automatically.
Part Six: The Limits of Static Roles
RBAC assumes that roles are relatively static — that users have roles, permissions are attached to those roles, and both change slowly. Modern systems challenge these assumptions in several important ways.
Dynamic Permission Requirements
Consider a document collaboration system. A user creates a document and shares it with specific people for a limited time. Some should be able to edit. Some should only view. Some should be able to comment.
RBAC struggles here because the permissions are tied to the relationship between a user and a specific resource, not to a static role. Alice is not always an editor. She is an editor for this specific document that Bob shared with her. This is resource-level authorization. RBAC alone cannot handle it — you need to combine RBAC with ownership or access control lists (ACLs).
Time-Bound Access
A contractor needs access for three months. A temporary employee needs access while a permanent employee is on leave. A compliance auditor needs access for a one-week review. RBAC can handle this by assigning roles with expiration dates, but many RBAC systems do not support time-bound assignments natively. Even when they do, you end up relying on manual cleanup that never happens.
Context-Aware Access
A user should be able to access sensitive data only from the corporate network. A financial transaction should require approval from two different managers. A user logging in from an unfamiliar device should have restricted permissions. RBAC does not account for context — it only knows the user's role, not the circumstances of the access attempt. Handling context requires policy-based approaches that consider environmental attributes.
Token-Embedded Roles and Stale State
In modern API-driven systems, roles are frequently embedded in signed tokens — JWTs, for example — issued at login time. This creates a subtle but important problem: if a user's roles change after their token is issued, the token still carries the old roles until it expires. A user who is demoted or has a role revoked may continue to hold those permissions for hours. This is not a flaw in RBAC itself, but it is a consequence of how RBAC is implemented at runtime that deserves careful attention in system design.
Least Privilege in Practice
RBAC makes least privilege difficult to achieve precisely. A user needs access to a specific report. RBAC says: assign them the "ReportReader" role. But that role might grant access to all reports, not just the one they need. To achieve true least privilege, you often need to grant permissions at the resource level, which is too granular for RBAC to handle cleanly.
Cross-Application Consistency
When a user has roles across multiple applications, understanding their effective permissions becomes complex. Does the "Admin" role in the CRM give them access to financial data in the ERP? Probably not — but assumptions form, and RBAC does not provide a unified view across applications. Each application maintains its own role model in isolation.
Part Seven: RBAC vs ABAC — When to Evolve
RBAC is not the end of the authorization journey. For many systems, it is the beginning.
ABAC — Attribute-Based Access Control — is the natural evolution when RBAC becomes too rigid or too complex. Where RBAC grants access based on a user's role, ABAC evaluates policies against attributes: who the user is, what resource they are accessing, what action they are taking, and what the environment looks like at that moment.
RBAC operates at role-level granularity with a relatively static structure. It is simple to reason about and fits well when permissions are stable and organizational hierarchies are clear. ABAC operates at attribute-level granularity with dynamic, context-sensitive policies. It is more complex to implement but handles fine-grained and conditional access decisions that would cause role explosion under RBAC.
Consider moving from RBAC to ABAC — or a hybrid of both — when you have role explosion that is hard to manage; when you need resource-level permissions (Alice can edit Document X but not Document Y); when you need time-bound or context-aware access; when permissions depend on attributes like location, device, or time of day; or when you are spending more time managing roles than building features.
RBAC remains the right choice when your permission model is simple and stable, when you have a small number of user types, when you do not need resource-level distinctions, or when you are integrating with systems that only support RBAC.
Most mature systems use both. RBAC handles the broad functional roles — Doctor, Nurse, Pharmacist — for high-level access decisions. ABAC handles fine-grained decisions within those roles, such as whether a doctor can access a specific patient's record based on department and care-team assignment.
Part Eight: RBAC in Different Contexts
RBAC manifests differently depending on the environment, though the core concepts remain consistent.
RBAC in Databases
PostgreSQL and other databases have native RBAC. You create roles, grant permissions to roles, and assign users to roles.
The same pattern exists in MySQL, Oracle, and SQL Server. Database RBAC is often the first place developers encounter role-based thinking, and it maps cleanly to the conceptual model.
RBAC in Kubernetes
Kubernetes RBAC uses Roles and ClusterRoles. A Role grants permissions within a namespace. A ClusterRole grants permissions across the entire cluster.
Users are bound to roles through RoleBindings and ClusterRoleBindings. The Kubernetes model is a clean example of RBAC applied to infrastructure rather than application data.
RBAC in Applications
Most web applications implement RBAC at the application layer. Permissions are stored in the database, and middleware checks the user's roles before allowing access to endpoints.
A better pattern — which the mistakes section covers — is checking for specific permissions rather than role names. This decouples authorization logic from role naming decisions and makes the system more resilient to role restructuring.
Part Nine: Common RBAC Mistakes
Roles as Permission Buckets
The problem: administrators create a role called "PowerUser" that contains every permission imaginable. Instead of assigning multiple focused roles, they assign one bloated role to avoid thinking about it.
The fix: keep roles focused. A user should have multiple roles if they need multiple functions. This keeps permissions transparent and least privilege achievable.
Role Explosion Without Cleanup
The problem: roles are created for one-off needs and never removed. The role list grows indefinitely. Nobody knows what half of them are for.
The fix: implement role lifecycle management. Roles should be reviewed quarterly. Unused roles should be archived. New roles should require approval with documented justification.
Confusing Roles with Groups
The problem: roles and groups are conflated. Groups are for organizing users — "Cardiology Department," "London Office." Roles are for permissions. Mixing them leads to confusion about what a role actually grants.
The fix: keep roles for permissions. Use separate constructs for organizing users.
Hardcoding Role Names
The problem: application code contains hardcoded role names like if user.role == "admin". When the role name changes or is restructured, the code breaks.
The fix: check for specific permissions, not role names. Whether the user has the "prescribe_medication" permission is a stable question. Whether they have the "Doctor" role is not — roles get renamed, split, and restructured. Checking permissions decouples authorization from role taxonomy.
No Permission Audit Trail
The problem: you cannot answer basic questions like "Which users have the Doctor role?" or "What permissions does Alice actually have?" This makes compliance and incident response painful.
The fix: implement symmetric RBAC with full query capabilities. Store assignments in a way that supports reverse lookups in both directions.
Ignoring Default Deny
The problem: the RBAC implementation grants access when no role explicitly denies it, or worse, when no role matches at all. This is the opposite of a sound security posture.
The fix: always implement default deny. If no role grants a permission, access is denied. This is the most important correctness property in any authorization system.
Wildcard Permissions
The problem: roles are granted broad wildcard permissions — all actions on all resources — for convenience. This is common in cloud IAM configurations and application-level admin roles.
The fix: be explicit. Grant the specific actions on the specific resources the role needs. Wildcards in authorization policies are a security risk waiting to be exploited.
Part Ten: RBAC and the Principle of Least Privilege
RBAC is often described as a mechanism for implementing least privilege. But RBAC alone does not guarantee least privilege — it only makes the problem more manageable than assigning permissions directly to individual users.
True "least privilege" within RBAC requires focused roles where each role contains only the permissions needed for that function; separation of duties so that critical functions are split across roles; regular review so that permissions do not silently accumulate; and temporary assignments so that time-limited needs use time-bound role grants rather than permanent ones.
Consider a customer support agent who needs to view customer orders but not edit them, and who can process refunds up to £100 but needs manager approval for larger amounts.
A naive implementation gives them one "Support" role with all permissions. A least-privilege implementation creates three separate roles: SupportReader can view orders and customer records; SupportRefunder can process refunds up to £100; SupportSupervisor can approve refunds over £100. A typical agent gets SupportReader and SupportRefunder. A supervisor gets SupportReader and SupportSupervisor. No single role is bloated. Permissions are transparent. Audits are meaningful.
This is what least privilege looks like in practice — not a single role that happens to be named carefully, but a composition of focused roles that together grant exactly what is needed and nothing more.
Part Eleven: The Future of RBAC
RBAC is not going away. It is too useful, too familiar, and too well-supported. But it is evolving.
RBAC + ABAC hybrids are increasingly the standard for mature systems. RBAC handles the broad strokes. ABAC handles fine-grained, context-sensitive decisions. A user has the "Doctor" role (RBAC), but they can only access patient records for patients assigned to their department (ABAC). The decision uses both the role and the patient-department attribute.
Externalized authorization is gaining traction. Instead of embedding authorization logic in each application, organizations are moving to centralized policy engines like OPA (Open Policy Agent). RBAC becomes one input to these policies rather than the entire authorization model. This makes cross-application consistency achievable and puts policy management in one place.
Dynamic roles are emerging in high-security systems — roles derived dynamically from attributes rather than assigned statically. A user's role might only be "Manager" when they are logged in from a trusted device during business hours. Outside those conditions, a more restricted role applies.
ReBAC (Relationship-Based Access Control) models permissions based on relationships between users and resources. This is common in collaboration systems, social networks, and document sharing. Google's Zanzibar system — used by Google Drive, Calendar, and YouTube — is the prominent example. A user can edit a document because they were directly granted edit access by the owner, or because they are a member of a group that was granted access. Zanzibar resolves the full relationship graph to make the decision. As more software is built around sharing and collaboration, ReBAC patterns will become increasingly relevant.
Part Twelve: What You Should Take Away
RBAC is the foundational authorization model for most systems — and for good reason. It aligns with how organizations think, simplifies administration, and scales reasonably well for a wide range of use cases.
After reading this article, you should be able to explain the core RBAC model and how users, roles, and permissions relate; design good roles that are focused, meaningful, and reusable; recognize the symptoms of role explosion and the practical steps to prevent it; understand the limits of static roles — resource-level permissions, time-bound access, token staleness, context sensitivity; identify when to evolve beyond RBAC to ABAC or hybrid approaches; implement RBAC correctly, avoiding bloated roles, hardcoded role names, wildcard permissions, and missing default deny; and apply least privilege principles through role composition rather than individual permission grants.
Most importantly, RBAC is a tool — not a destination. When your system outgrows it, the right response is not to force RBAC into problems it cannot solve, but to layer in the models that can.
Closing: The Hospital Revisited
Let us return to the hospital.
For years, RBAC served it well. Doctors had the doctor role. Nurses had the nurse role. Administrators had the admin role. New employees were onboarded quickly. Audits were straightforward. The system was understood by everyone who worked with it.
But then the hospital grew. It added specialty clinics, opened satellite locations, integrated with external labs, and started sharing patient data with research institutions.
The doctor role became bloated. A cardiologist and a radiologist and a pediatrician all had the same role, but they needed different data. Role explosion began: DoctorCardiology, DoctorRadiology, DoctorPediatrics, DoctorCardiologyAttending, DoctorRadiologyFellow. The list kept growing. Nobody could explain why half the roles existed. Zombie roles accumulated. Audits became exercises in archaeology.
The hospital needed access based on department, patient assignment, shift, and location. RBAC alone could not handle this complexity.
So the hospital did not abandon RBAC. It evolved. It kept the broad functional roles — Doctor, Nurse, Pharmacist — for high-level access decisions. It added attribute-based controls for fine-grained ones. A doctor could access a patient's record only if they were assigned to that patient's care team. A nurse could administer medication only during their assigned shift. A researcher could view anonymized data but never identifiable patient information.
RBAC provided the structure. ABAC provided the flexibility. Neither was sufficient alone.
Your system will likely follow a similar path. Start with RBAC. Keep roles focused. Prevent explosion before it starts. And when the limits of static roles become painful — when roles are multiplying faster than you can manage them, when permissions need to be resource-specific, when context starts to matter — evolve.
Authorization is not static. Neither should your approach be.
About N Sharma
Lead Architect at StackAndSystemN Sharma is a technologist with over 28 years of experience in software engineering, system architecture, and technology consulting. He holds a Bachelor’s degree in Engineering, a DBF, and an MBA. His work focuses on research-driven technology education—explaining software architecture, system design, and development practices through structured tutorials designed to help engineers build reliable, scalable systems.
Disclaimer
This article is for educational purposes only. Assistance from AI-powered generative tools was taken to format and improve language flow. While we strive for accuracy, this content may contain errors or omissions and should be independently verified.
